Get rid of Thor ransomware and decrypt .thor extension files
This is a comprehensive report on the Thor release of the Locky ransomware that encompasses all symptoms of this injection and provides steps to decrypt .thor files.
The ransomware strain called Locky has mutated several times over the course of this year. The sub-versions dubbed Zepto and Odin demonstrated that the threat actors were not going to abandon their cyber racketeering campaign or leave the code in its original shape at the mercy of security researchers’ increasingly successful work. The latest update has brought about another set of changes. Referred to as the Thor virus as per the extension being appended to victims’ files, the current spinoff is different from its precursors both externally and internally, that is, on a behavioral level. The most drastic modification has to do with the Trojan’s offline encryption capacity, where it can lock down one’s data without querying its Command and Control server for the crypto key. This approach poses an additional hurdle for detection, because firewalls and anti-ransomware modules of security suites are now less likely to detect the infection based on its suspicious Internet traffic patterns.
Despite the high sophistication of its code and modus operandi, the Thor ransomware is proliferating via old school methods. In particular, spam serves as the medium for contamination. In order to generate as many rogue emails as possible within a minimum time span, the criminals are in cahoots with operators of the so-called Necurs botnet, one of today’s largest malware spreading networks. The spam messages delivering the Thor iteration of Locky are tailored to thwart sandboxing and evade AVs. The subject and body of such an email usually suggest urgency. For instance, the whole thing may look like an invoice, cancellation request, job offer, resume, receipt, or a scanned image of some sort. In fact, extracting the attached ZIP file will execute an obfuscated JavaScript, HTA or VBScript entity which, in its turn, triggers the Thor contamination chain.
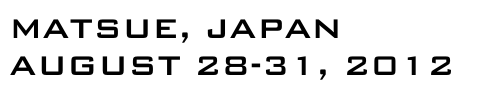
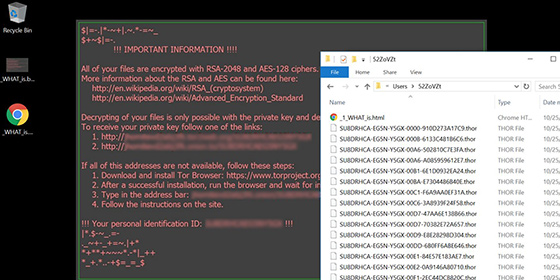
The complexity of this ransomware’s crypto facet revolves around two different algorithms used in a tandem. These are the asymmetric RSA-2048 and symmetric AES-128 standards. Again, the newest edition of Locky has a complete set of encryption keys already embedded in its binary, therefore the data encoding process will take place even if a victim disconnects the machine from the Internet. The Trojan scrambles all personal files located on the HDD, removable drives and network shares. Aside from making these entries inaccessible, it also turns filenames into unrecognizable strings like TS7DRJCN-FD4M-Z6GW-00D2-6244D482B7C7.thor. The ransom notes named _WHAT_is.html and _WHAT_is.bmp contain several links to visit one’s personal decryption hub called the Locky Decryptor page. Said resource also informs the user how much they need to pay and what Bitcoin address they must submit the cryptocurrency to. The ransom is 0.5 BTC, which is the equivalent of about $350. Paying that much money for being able to access one’s proprietary data is a hateful deal, so focus on alternative file restoration method outlined below.
Thor ransomware removal
It’s usually quite easy to get rid of the offending program proper. Ransom Trojans are easy targets for antimalware suites once the data encryption part has been performed. This fact alone does not set aside the necessity of removing the infection, because it may cause further damage along with the likely escorting modules such as password stealers.
1. Download, install and run Thor removal software. Click the Start New Scan button and wait until the suite does a thorough system checkup.
Download .thor file virus remover2. When the scan results are readily available, go to Fix Threats and let the program do its cleaning job.
Workarounds to recover .thor encrypted files
Unless security researchers or AV labs release a dependable decrypt tool, recovering the scrambled files is somewhat of a lottery. However, there are techniques that ransomware victims shouldn’t fail to try before considering the buyout suggested by the criminals. Be sure to peruse and implement the methods below.
1. Backups
First and foremost, download backup copies of your important data from an offsite storage unaffected by the ransomware. In case you hadn’t had a backup strategy before the breach occurred,
proceed to the next step. Also, start maintaining secure backups of the most valuable information so that attacks like this one won’t cause that much damage in the future.
2. Shadow Copies
Thor is coded to obliterate Shadow Copies of its victim’s files, which are data snapshots automatically made by the operating system. The ransomware has reportedly failed to complete
this task in some cases, though. An important prerequisite of successful recovery is the ‘enabled’ status of the System Restore feature prior to the compromise. There are two ways
to take advantage of this functionality built into Windows.
- Previous Versions Based on Restore Points
Select a random encrypted file, right-click on it and go to Properties. Now proceed to the Previous Versions tab. If the OS had been making snapshots of this file during system restore events, it will display the list of available file versions. Highlight the latest one and select Copy to recover it to a new path on the computer. Clicking the Restore button will reinstate the file to its original location.

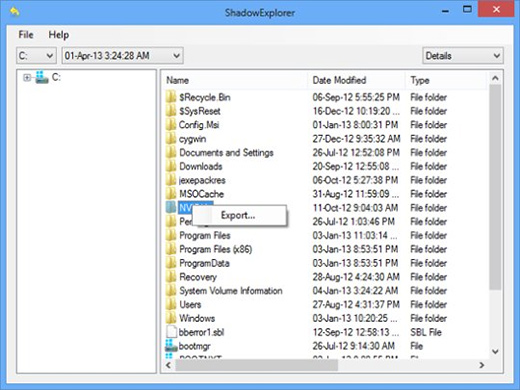
- ShadowExplorer
The applet called ShadowExplorer is meant to automate data recovery based on VSS (Volume Snapshot Service). If that’s the workflow of your choice, download and install the tool. Run it, select the local drive name and the folder of interest, right-click on it, hit the Export option and follow further prompts to get the job done.
3. Forensic Tools
The algorithm of data scrambling employed by most ransomware involves the deletion of original files, while their encrypted copies are the objects of the ransom bargain. Now, erasing
information off the hard drive is only irreversible when done with multiple overwrites. Otherwise, it may be possible to restore files using utilities like
Data Recovery Pro. Simply run the app and see whether it can do the trick.
Look before you leap into secure computing
Now that you have hopefully recovered your files, make sure the Thor ransomware will make no more trouble. Consider scanning the system for executables and leftover registry keys added by the infection. Double-checking is also a good idea because some of the newer variants of crypto malware are accompanied by other threats such as rootkits and identity theft programs. So run the scan again and see whether or not you are completely safe.