Decrypt RSA-4096 ransomware virus
Use this guide to remove RSA-4096 CryptXXX virus from Windows computer and restore files it encrypted with the strong asymmetric cryptosystem.
RSA-4096 per se is a benign concept that denotes a cryptographic standard that uses different pieces of secret data, known as keys, for the data encoding and decoding operations. The reason why this public-key crypto algorithm is being often associated with something malicious is that a ransomware sample called CryptXXX, or UltraCrypter, refers to it as the mode of file locking. One way or another, it’s important to make this disambiguation from the start. Let’s move on. The extortionists who operate online can only conduct a successful attack as long as they implement some cipher to scramble one’s personal data. This is precisely what the above-mentioned strain does, employing RSA-4096 as the main mechanism for achieving this goal.
The main channel through which the CryptXXX ransomware is distributed involves exploit kits. This offensive methodology relies on several factors, one of which is the presence of outdated software on a one’s machine. Outdated often means vulnerable, especially if it’s a solution like Adobe Flash Player or Java. When the user of a PC running such unpatched programs visits a compromised web page, the previously deposited script redirects them to the exploit kit’s domain. Then, the EK automatically detects unpatched software in the target system and exploits those security flaws to inject the malicious code. The random-named executable features obfuscation capabilities that prevent antiviruses from intercepting it.

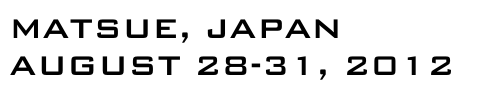
The next stage of the attack includes a scan of all fixed, removable and network drives for popular types of data. When a file with one of the widespread extensions is found, the ransomware uses RSA-4096 algo to encrypt it. Furthermore, the newest version of CryptXXX also changes filenames, turning them into random strings of symbols followed by arbitrary extensions. The user gets recovery instructions via a tandem of ransom notes dropped onto the computer in different formats, including README.html, README.txt and README.bmp.
The warning notification in these notes is as follows: “All of your files were protected by a strong encryption with RSA-4096 … Specially for your PC was generated personal RSA4096 key, both public and private. ALL YOUR FILES were encrypted with the public key, which has been transferred to your computer via the Internet. Decrypting of your files is only possible with the help of the private key and decrypt program, which is on our secret server.” Unfortunately, this information is true-to-life. The criminals suggest that you buy the private key for about 500 USD. This ransom is payable in Bitcoins only, where the size is 1.2 BTC. If the victim doesn’t fit in the deadline, usually 100 hours, the ransom will increase to 2.4 BTC.
The recovery option imposed by the perpetrators isn’t the only applicable one. A couple of forensic techniques that don’t involve any payment may come in handy. See below for further details on file restoration.
RSA-4096 ransomware removal
It’s usually quite easy to get rid of the offending program proper. Ransom Trojans are easy targets for antimalware suites once the data encryption part has been performed. This fact alone does not set aside the necessity of removing the infection, because it may cause further damage along with the likely escorting modules such as password stealers.
1. Download, install and run RSA-4096 removal software. Click the Start New Scan button and wait until the suite does a thorough system checkup.
Download RSA-4096 ransomware remover2. When the scan results are readily available, go to Fix Threats and let the program do its cleaning job.
Workarounds to recover RSA-4096 encrypted files
Unless security researchers or AV labs release a dependable decrypt tool, recovering the scrambled files is somewhat of a lottery. However, there are techniques that ransomware victims shouldn’t fail to try before considering the buyout suggested by the criminals. Be sure to peruse and implement the methods below.
1. Backups
First and foremost, download backup copies of your important data from an offsite storage unaffected by the ransomware. In case you hadn’t had a backup strategy before the breach occurred,
proceed to the next step. Also, start maintaining secure backups of the most valuable information so that attacks like this one won’t cause that much damage in the future.
2. Shadow Copies
CryptXXX is coded to obliterate Shadow Copies of its victim’s files, which are data snapshots automatically made by the operating system. The ransomware has reportedly failed to complete
this task in some cases, though. An important prerequisite of successful recovery is the ‘enabled’ status of the System Restore feature prior to the compromise. There are two ways to
take advantage of this functionality built into Windows.
- Previous Versions Based on Restore Points
Select a random encrypted file, right-click on it and go to Properties. Now proceed to the Previous Versions tab. If the OS had been making snapshots of this file during system restore events, it will display the list of available file versions. Highlight the latest one and select Copy to recover it to a new path on the computer. Clicking the Restore button will reinstate the file to its original location.

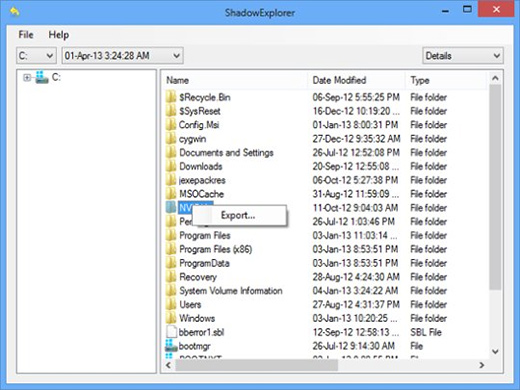
- ShadowExplorer
The applet called ShadowExplorer is meant to automate data recovery based on VSS (Volume Snapshot Service). If that’s the workflow of your choice, download and install the tool. Run it, select the local drive name and the folder of interest, right-click on it, hit the Export option and follow further prompts to get the job done.
3. Forensic Tools
The algorithm of data scrambling employed by most ransomware involves the deletion of original files, while their encrypted copies are the objects of the ransom bargain. Now, erasing
information off the hard drive is only irreversible when done with multiple overwrites. Otherwise, it may be possible to restore files using utilities like
Data Recovery Pro. Simply run the app and see whether it can do the trick.
Look before you leap into secure computing
Now that you have hopefully recovered your files, make sure the RSA-4096 ransomware will make no more trouble. Consider scanning the system for executables and leftover registry keys added by the infection. Double-checking is also a good idea because some of the newer variants of crypto malware are accompanied by other threats such as rootkits and identity theft programs. So run the scan again and see whether or not you are completely safe.